Anti-virus software is not the be and end all of protection – many, including Canonical, will argue that you do not even need anti-virus on Linux. Repositories maintained by distributions make it more difficult to install dodgy software, while a preference for open source makes it easier for anyone to vet a package.
Yet, in recent years, the volume and complexity of malware targeting Linux systems has risen substantially and it is now not as easy to identify malicious activity manually. Attackers like to target Linux servers, often not as their primary target but as a vessel to spread malware to more profitable Windows devices.
So, if you want to protect your users and the general internet population, anti-virus is not a terrible idea. At the same time, you'll be reducing the risk that newer strains targeting the growth in Linux desktops (Chromebook, SteamDeck, WSL, etc.) will infect your server with cryptojackers, etc. should a server admin fail to execute good security practice.
Though the industry is not as developed on Linux as it is on Windows PCs, there are still plenty of Linux antivirus options. We'll round up some of the best free antiviruses for Linux, and then move on to paid solutions.
The best free antivirus for Linux
The number of free antiviruses on Linux is limited due to the reduced threat to home users. Most commonly, Linux antivirus tools are installed in enterprise environments where they are required by policy or compliance. Still, there are a couple of free antiviruses, and one in particular that is recommended again and again.
ClamAV
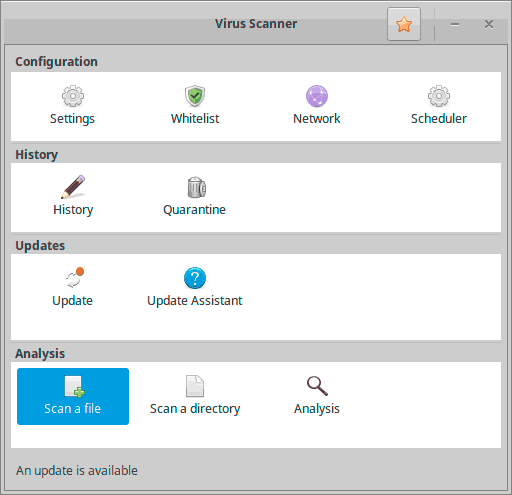
ClamAV is the most commonly recommended free Linux antivirus. It is free and open source, uses and tends to catch over 95% of known malware samples. The idea is to provide protection at the most common interfaces where viruses spread, such as email and the browser. There is also a GUI, ClamTk, which makes it much more accessible to non-technical users.
Additionally, and this is key, it is lightweight. It uses very little CPU resources but is still able to detect rootkits, trojans, worms, etc. It's not perfect, however:
- Its detection rate isn't that great
- You'll probably run into a lot of false positives (though this is true of most Linux AV)
- It detects viruses by checking against a database of file hashes rather than analyzing behavior. This means malware authors just need to change the source code a little for it to be temporarily undetected again.
Overall, we can recommend ClamAV for users who want a lightweight antivirus that they can "set and forget". It's probably all non-business users need (if they need anything at all).
RootKit Hunter (RKHunter)
RKHunter is the most popular command-line rootkit detector on Linux. Like most free Linux antiviruses it has its failings, which are primarily rooted in its signature-based detection. However, as well as looking for rootkits via signature, RKHunter looks for general changes that may be indicative of malware, such as backdoor ports, root equivalent accounts, etc. It will also warn you of some issues with your security configuration.
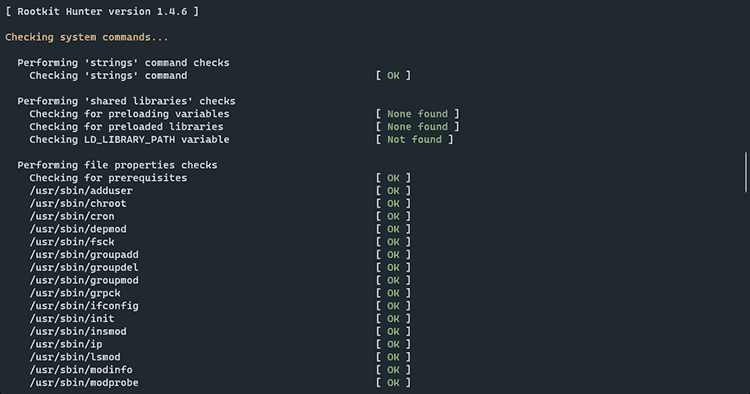
Overall, it is a useful free tool to discover factors that bear closer investigation, though you should be aware that false positives are not uncommon and run it from LiveCD or in your provider's rescue mode for the best results.
ChkrootKit
ChkrootKit is another rootkit detector, and it appears to be updated more frequently than the popular RKHunter. The tool checks system binaries, interfaces, etc. for rootkits and LKM trojans, while checking logs for signs of tampering. It can currently detect a total of 72 rootkits.
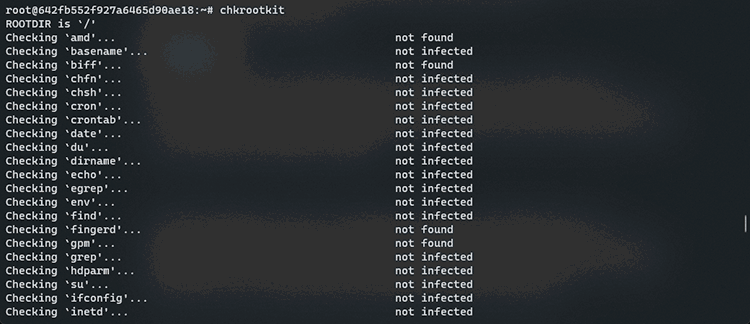
Just like RKHunter, however, ChkrootKit operates by looking for known signatures. This means that an attacker can modify the rootkit sources to change its signature and avoid detection. For this Chkrootkit has an expert mode, which allows users to view suspicious strings inside a binary themselves.
YARA
YARA is more aimed at researchers than the general public, but it is still a very useful command-line pattern-matching tool for malware detection. Researchers create descriptions of malware using textual of binary patterns, forming a set of rules (and signatures) that YARA can use to detect malware and identify new strains.
Non-researchers, however, don't need to create their own rules. They can instead download rules from a massive repository that includes contributions from ESET, AlienVault, Apple, FireEye, McAfee, and more. These can range from a collection of common threats to rules designed to check for specific new malware.
The best paid antivirus for Linux
If you want to move past basic (and frankly outdated) signature-based malware protection on Linux, you'll have to pay. The best antivirus tools on Linux are aimed at the enterprise, and can be quite pricey. The protection, you get, however, tends to be leaps and bounds ahead of the free options.
Microsoft Defender ATP/Microsoft Defender for Endpoint
Microsoft is no stranger to antivirus, but until a few years ago, it has been a stranger to antivirus on Linux. Microsoft Defender Advanced Threat Protection (ATP) was released in 2020 on RHEL, CentOS, Ubuntu, SLES, Debian, and Oracle. It is now part of Microsoft Defender for Endpoint and available as part of Microsoft Defender for Business and Microsoft 365 Business Premium plans.
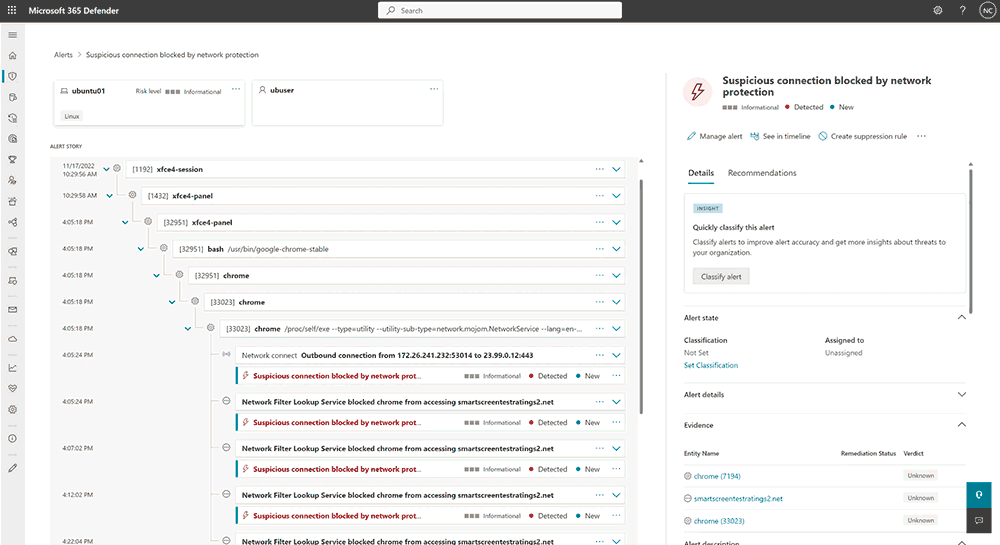
Many, of course, will wonder why they should trust the company that created Windows with the security of their Linux device. However, it does make a certain amount of sense. If somebody hacks your server to spread malware to Windows users, an antivirus that is very good at detecting Windows threats might be a good idea.
Additionally, Defender for Endpoint leans heavily on behavior-based, heuristic detection. Rather than just checking whether malware matches a signature in a database, it looks at what applications are supposed to be doing, what they are actually doing, and whether their code has suspicious properties. This allows it to detect malware and viruses that aren't yet known to researchers, as well as variants of already existing viruses that have been changed to avoid protection.
CrowdStrike Falcon
CrowdStrike Falcon is another Endpoint security tool that supports both Windows and Linux. It uses machine learning and AI to detect both known and unknown malware by identifying and acting on malicious behavior. CrowdStrike is able to block exploits and fileless attacks and isolate malicious files as soon as they appear on the host machine. By all counts, it is very effective at what it does with few false positives and good human support for those on higher subscription tiers.
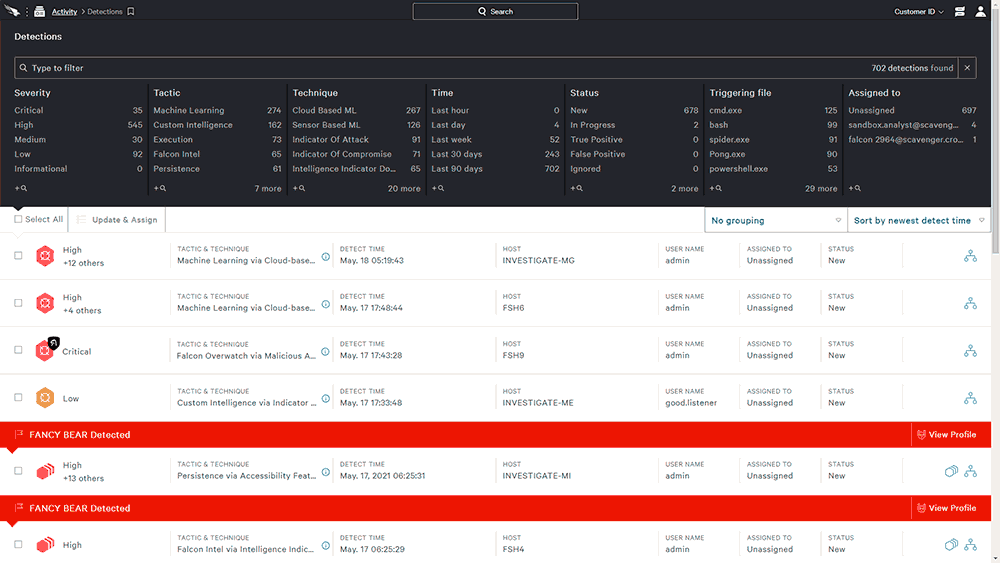
Though Microsoft Defender for Endpoint will still do a great job (and is likely the right pick if you're already invested in the Microsoft ecosystem), CrowdStrike has a simpler UI and easier deployment on Linux. Its basic "Falcon Go" plan starts at $300 per year, while its $500 "Pro" plan offers additional threat intelligence and firewall features. If you have the budget, it's well worth considering.
BitDefender GravityZone
BitDefender GravityZone, previously BitDefender Endpoint Protection, is another enterprise-focused machine learning-based antivirus for Linux, Windows, and macOS. Like CrowdStrike, it can prevent file-less attacks before they are executed and predict and block attacks before they happen. Files that require further analysis are sent to its sandbox analyzer, where they are automatically acted upon if there are suspicious findings.
Most major Linux server distros are supported, including Ubuntu, RHEL/CentOS, SUSE, Debian, Fedora, Oracle, etc. However, it is worth noting that some GravityZone users report high resource usage on Linux servers without additional tweaking and a tendency to act on false positives. It is likely not as good as Crowdstrike, but in most cases, it will do a good enough job and cost you less.
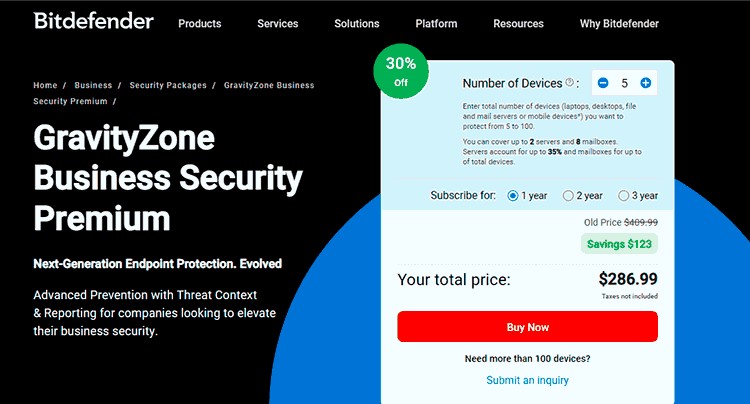
Another perk of GravityZone is its reasonable and flexible pricing, which allows you to choose the number of devices and time period. This makes it more approachable for small businesses.
